Your apps are spying on you
Published 18-JAN-2019 16:22 P.M.
|
3 minute read
Hey! Looks like you have stumbled on the section of our website where we have archived articles from our old business model.
In 2019 the original founding team returned to run Next Investors, we changed our business model to only write about stocks we carefully research and are invested in for the long term.
The below articles were written under our previous business model. We have kept these articles online here for your reference.
Our new mission is to build a high performing ASX micro cap investment portfolio and share our research, analysis and investment strategy with our readers.
Click Here to View Latest Articles
Awareness around data integrity is improving every day, but are your efforts to shore up your sensitive personal information in vain?
Unfortunately, the answer appears to be yes.
Have you ever had a phone conversation about a brand or product, only to hop onto your browser later that day and be inundated with ads for the same product?
It's enough to make anyone do a double take, and it's been the source of an old legend: our phones record our conversations.
The result?
9,000 of those apps had the potential to be unfaithful to the user.
While no evidence was found of recorded conversations, the apps in question took screenshots of activity before forwarding them onto third parties.

That’s just a tad horrifying.
David Choffnes, who was one of two computer science professors who oversaw the study, commented on the findings: “We found that thousands of popular apps have the ability to record your screen and anything you type.
“That does include your username and password, because it can record the characters you type before they turn into those little black dots.”
“We knew we were looking for a needle in a haystack,” Choffnes said, “and we were surprised to find several needles.”
Although the privacy breaches over the course of the study were largely benign, it drives home just how easy it could be for your phone to be exploited for cash.
“This opening will almost certainly be used for malicious purposes, it’s simple to install and collect this information,” said Christo Wilson, the other computer science professor on the research team.
“And what’s most disturbing is that this occurs with no notifications to or permission by users.
“In the case we caught, the information sent to a third party was zip codes, but it could just as easily have been credit card numbers.”
It should be noted that while the study was only conducted on Android apps, the study concluded that iOS apps were likely guilty of similar breaches.
So, how do we combat this betrayal?
Android Q teases new and improved privacy controls
While there’s no quick fix for this loophole, greater app security is a major point of emphasis in the upcoming Android Q release.
In the new edition of the popular OS, a status bar feature displays when sensitive phone permissions are in use and which apps are responsible.
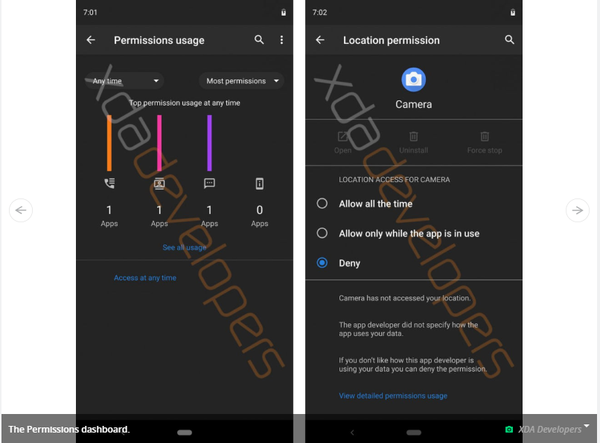
Among these fresh features will be a list that displays:
- Apps by most frequently accessed permission
- Apps by most permission use
- Apps that gained recent permission access
This will be a significant upgrade over Android’s current permission screen, which is a simple series of on/off switches.
Other improvements include greater visibility on why apps need certain permissions and GPS services being actively turned off when an app is running in the background.
In theory, these updates should help users make informed decisions around which apps could be up to no good.
General Information Only
S3 Consortium Pty Ltd (S3, ‘we’, ‘us’, ‘our’) (CAR No. 433913) is a corporate authorised representative of LeMessurier Securities Pty Ltd (AFSL No. 296877). The information contained in this article is general information and is for informational purposes only. Any advice is general advice only. Any advice contained in this article does not constitute personal advice and S3 has not taken into consideration your personal objectives, financial situation or needs. Please seek your own independent professional advice before making any financial investment decision. Those persons acting upon information contained in this article do so entirely at their own risk.
Conflicts of Interest Notice
S3 and its associated entities may hold investments in companies featured in its articles, including through being paid in the securities of the companies we provide commentary on. We disclose the securities held in relation to a particular company that we provide commentary on. Refer to our Disclosure Policy for information on our self-imposed trading blackouts, hold conditions and de-risking (sell conditions) which seek to mitigate against any potential conflicts of interest.
Publication Notice and Disclaimer
The information contained in this article is current as at the publication date. At the time of publishing, the information contained in this article is based on sources which are available in the public domain that we consider to be reliable, and our own analysis of those sources. The views of the author may not reflect the views of the AFSL holder. Any decision by you to purchase securities in the companies featured in this article should be done so after you have sought your own independent professional advice regarding this information and made your own inquiries as to the validity of any information in this article.
Any forward-looking statements contained in this article are not guarantees or predictions of future performance, and involve known and unknown risks, uncertainties and other factors, many of which are beyond our control, and which may cause actual results or performance of companies featured to differ materially from those expressed in the statements contained in this article. S3 cannot and does not give any assurance that the results or performance expressed or implied by any forward-looking statements contained in this article will actually occur and readers are cautioned not to put undue reliance on forward-looking statements.
This article may include references to our past investing performance. Past performance is not a reliable indicator of our future investing performance.
