Hackers continue to play a Game of Thrones
Published 10-AUG-2017 15:23 P.M.
|
4 minute read
Hey! Looks like you have stumbled on the section of our website where we have archived articles from our old business model.
In 2019 the original founding team returned to run Next Investors, we changed our business model to only write about stocks we carefully research and are invested in for the long term.
The below articles were written under our previous business model. We have kept these articles online here for your reference.
Our new mission is to build a high performing ASX micro cap investment portfolio and share our research, analysis and investment strategy with our readers.
Click Here to View Latest Articles
By now you would have heard of ‘Mr Smith’. This particular Mr Smith is not your next door neighbour; nor one of the billions with that name going about their daily business. No, this Mr Smith is using the generic ‘Smith’ moniker in a gameplay that would have the most evil and manipulative Game of Thrones characters jostling to put him on their counsel.
The Game of Thrones context here is no coincidence. Mr Smith, if you don’t know by now, is the shadowy figure behind the biggest email hack since Sony was infiltrated in 2014.
On November 25, 2014, a group calling itself GOP or The Guardians of Peace, hacked their way into Sony Pictures, leaving the Sony network crippled for days. They stole valuable insider information including previously unreleased films posted to the Internet and the personal details of staff and network stars. There were also vague allegations North Korea was behind the attack as retribution for the James Franco, Seth Rogen movie titled ‘The Interview’.
The Sony leak was one of the biggest scandals of the year. The company confirmed costs of $15 million to repair and investigate the November cyberattack.
Costs to business in general can be crippling. If you are not a multi-billion dollar company such as Sony or HBO, an attack has the potential to shut a business down.
According to Steve Langan, chief executive at Hiscox Insurance, “cybercrime cost the global economy over $450 billion, over 2 billion personal records were stolen and in the US alone over 100 million Americans had their medical records stolen.”
Only 30 per cent of companies cyber-attack ready
Hiscox Insurance released the Cyber Readiness Report 2017 in February this year and surveyed 3,000 companies across three countries to assess their readiness to deal with cybercrime in terms of strategy, resourcing, technology and process.
The findings are concerning with 53 percent of the companies assessed found to be ill-prepared to deal with an attack, and just 30 percent rated as “expert” in their overall cyber readiness.
The figures are backed by Lloyd’s of London which in 2015 estimated that cyberattacks cost businesses as much as $400 billion a year, which includes direct damage plus post-attack disruption to the normal course of business.
According to Forbes, some vendor and media forecasts over the past year put the cybercrime figure as high as $500 billion and more.
Whilst the issue is well reported, it is still not front of the queue in terms of finding an easy fix.
“It’s easy to assume that your email security solution is protecting you from advanced attacks. If you don’t have visibility into what’s actually getting delivered to the inboxes of employees, why would you think otherwise?” said Ed Jennings, chief operating officer at cyber security solutions firm Mimecast.
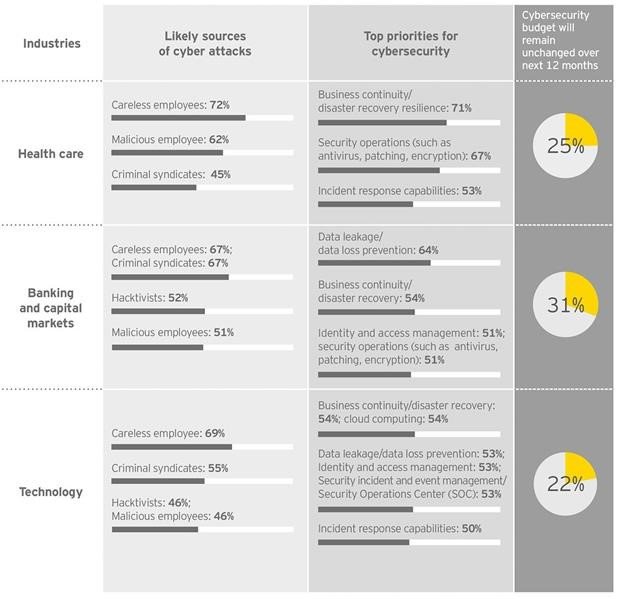
Backing this theory is Richard Watson, EY Oceania Cyber Leader who said, while it was clear the internal risks posed by employees was a serious concern for many Australian businesses, remedial action is not yet enough of an organisational priority.
“If businesses want to avoid the potentially significant monetary and reputational risks associated with a breach or attack resulting from staff carelessness, they need to invest in proper training – particularly when it comes to the safe use of mobile devices.
“While employees currently present the greatest risk to Australian organisations, as the front line of every organisation’s cyber defence, they also present the greatest opportunity to increase a business’s cyber resilience,” Mr Watson said.
The recent attack on HBO has once again highlighted the need for vigilance; though it shouldn’t take a high profile case such as this one to do so.
Mr Smith released personal phone numbers of actors, emails and scripts and is demanding a multimillion-dollar ransom to prevent the release of whole TV shows and further emails.
Cersei Lannister would be proud.
Mr Smith also sent a video message to HBO chief executive Richard Plepler telling him to pay up within three days or they would put online more HBO shows and confidential corporate data.
HBO said that it doesn’t believe its email system as a whole has been compromised, although it did acknowledge the theft of “proprietary information”.
That kind of spin is worthy of Tyrion Lannister.
The terms of Mr Smith’s blackmail
Given Mr Smith demanded “our six-month salary in bitcoin”, claiming they earn $12 million to $15 million a year from blackmailing organisations whose networks they have breached. They also said they would only deal directly with “Richard” and only send one “letter” detailing how to pay – adding that perhaps the HBO boss should be taking things more seriously.
Cybersecurity hacks are a major problem of our time. The companies with the best chance of avoidance are those that take the problem seriously and build resilience into the organisation. Whilst businesses can’t stop them completely, they can put up the shields and defend against the dragons – so to speak.
The bottom line: keep your emails close and your Mr Smiths far, far away.
General Information Only
S3 Consortium Pty Ltd (S3, ‘we’, ‘us’, ‘our’) (CAR No. 433913) is a corporate authorised representative of LeMessurier Securities Pty Ltd (AFSL No. 296877). The information contained in this article is general information and is for informational purposes only. Any advice is general advice only. Any advice contained in this article does not constitute personal advice and S3 has not taken into consideration your personal objectives, financial situation or needs. Please seek your own independent professional advice before making any financial investment decision. Those persons acting upon information contained in this article do so entirely at their own risk.
Conflicts of Interest Notice
S3 and its associated entities may hold investments in companies featured in its articles, including through being paid in the securities of the companies we provide commentary on. We disclose the securities held in relation to a particular company that we provide commentary on. Refer to our Disclosure Policy for information on our self-imposed trading blackouts, hold conditions and de-risking (sell conditions) which seek to mitigate against any potential conflicts of interest.
Publication Notice and Disclaimer
The information contained in this article is current as at the publication date. At the time of publishing, the information contained in this article is based on sources which are available in the public domain that we consider to be reliable, and our own analysis of those sources. The views of the author may not reflect the views of the AFSL holder. Any decision by you to purchase securities in the companies featured in this article should be done so after you have sought your own independent professional advice regarding this information and made your own inquiries as to the validity of any information in this article.
Any forward-looking statements contained in this article are not guarantees or predictions of future performance, and involve known and unknown risks, uncertainties and other factors, many of which are beyond our control, and which may cause actual results or performance of companies featured to differ materially from those expressed in the statements contained in this article. S3 cannot and does not give any assurance that the results or performance expressed or implied by any forward-looking statements contained in this article will actually occur and readers are cautioned not to put undue reliance on forward-looking statements.
This article may include references to our past investing performance. Past performance is not a reliable indicator of our future investing performance.